
Cryptography is a term that is derived from the Greek words “kryptos” meaning “hidden” and “graphein” which means “to write”. In other words cryptography involves hidden words or the study of information hiding and verification that includes the use of algorithms, protocols and strategies to consistently and securely delay or prevent access to sensitive information by unauthorized persons while enabling verifiability of all components in a communication. Cryptography allows people to transmit or store sensitive information over insecure networks such as the internet in way that it cannot be read by an unauthorized person except its intended recipient. This article is an introduction to cryptography with all that you need to know.
Main Goals of Cryptography:
Cryptography is used by security professionals for various reasons but the three main goals of cryptography include:
- Data confidentiality
- Data integrity
- Data authentication
Confidentiality or data privacy is the most important goal of cryptography hence the meaning of a message is encoded to conceal it. The sender uses a cryptographic key to encrypt the message and the recipient also uses the same or a different cryptographic key to decrypt or decode the message.
Data integrity involves ensuring that the message received is similar to the sent message I.e it has not been modified or altered in any way. A unique message digest is created using hashing from the sent message and using the same technique, the recipient creates a second digest from the received message for comparison with the original one. This technique prevents unintentional alteration of a message but a variation will help in the creation of digital signatures to prevent malicious alteration.
Data authentication involves verifying that data actually came from where it claims to come from which is accomplished with the help of digital certificates.
Cryptography has implementation in many fields including the latest blockchain technology, you can find a good reference on blockchain technology following blockchain online course here.
How Cryptographic Keys Work?
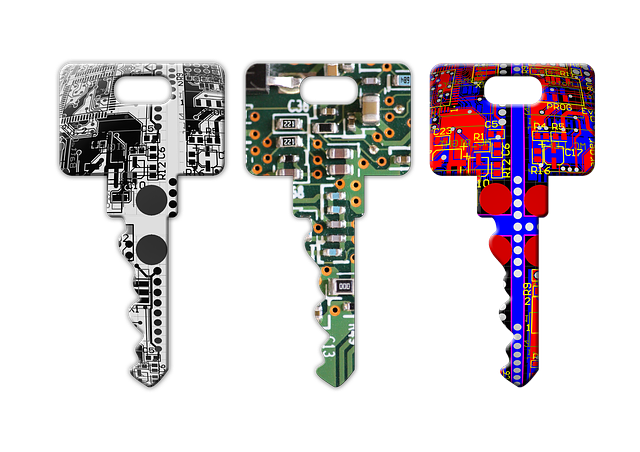 A cryptographic key is the most important part of a cryptographic operation since it is used to transform cipher text into plain text or vise versa with the help of a cryptographic algorithm. A cryptographic key is private ensuring secure communication. The security of a well designed cryptographic scheme entirely depends on how secure the keys used are. Cryptographic keys can be asymmetric or symmetric where symmetric encryption only requires one key while asymmetric encryption requires two different keys (One for encryption and the other for decryption). Public or private key pairs are provided by a certificate authority (CA) that uses the public key infrastructure.
A cryptographic key is the most important part of a cryptographic operation since it is used to transform cipher text into plain text or vise versa with the help of a cryptographic algorithm. A cryptographic key is private ensuring secure communication. The security of a well designed cryptographic scheme entirely depends on how secure the keys used are. Cryptographic keys can be asymmetric or symmetric where symmetric encryption only requires one key while asymmetric encryption requires two different keys (One for encryption and the other for decryption). Public or private key pairs are provided by a certificate authority (CA) that uses the public key infrastructure.
Cryptographic Algorithm:
A cryptographic algorithm or a cipher is simply the means used to alter data from plaintext (readable form) to ciphertext or a protected form and vise versa. Altering ciphertext into plaintext is referred to as encryption whereas altering ciphertext into plaintext is referred to as decryption.
Why Cryptography Is So Important?
Cryptography is extremely vital in IT security in order to achieve data integrity, data confidentiality, non-repudiation as well as user authenticity. Using cryptography, data is protected from unauthorized access or theft. It can be easy to forge an email but it is difficult to corrupt a digitally signed email. Sensitive information remains secret especially when it is sent over insecure networks like the internet. When sending data to someone, it is easy to ensure that only the recipient can be able to decrypt your message.
I have tried to cover maximum about the basics of cryptography and hopefully the reader will have good understanding of the basics that can be further flourished using more related cryptography tutorials.
